Solving Manual execution in M365 or Google Workspace is time-consuming with Effective Shared Mailbox & Permission Grants
Most MSPs do not have a mailbox problem. You have an execution problem. People search for “Solving Manual execution in M365 or Google Workspace is time-consuming with Effective Shared Mailbox & Permission Grants” because they feel that pain daily. It is not that you do not know how to grant access. It is the ten tiny steps, the chases, the swivel between consoles, and the updates that burn time and margin.
I have watched this pattern in a lot of shops. A simple “add me to finance@” eats 10 to 15 minutes when you add up identity matching, approval pings, mailbox permission changes, PSA notes, and the user message. One or two a day feels fine. Forty a week across tenants is where you lose hours, miss SLAs, and start dreading after-hours.
Key Takeaways:
- Manual mailbox and group permission grants waste 10–15 minutes per ticket and compound across tenants
- The real blocker is execution friction, not knowledge, especially approval chases and cross-tool steps
- Quantify the cost: dozens of tickets a week equals 50–100 tech hours a month you will never get back
- Emotion matters: the 5 pm stack, the weekend page, the constant context switching
- New way: lead with approver truth, act across M365 and Google Workspace from one flow, close the loop automatically
- Safe autonomy is the unlock: approvals inline, L1 actions across your stack, full audit without new dashboards
Shared Mailbox Access Should Not Take 15 Minutes Per User
Shared mailbox and group access can and should complete in under two minutes for common cases. The steps are well known, the risk is low, and the outcome is binary. When it takes 10–15 minutes, the delay comes from chasing approvals and hopping tools, not from technical difficulty.
I am not arguing for recklessness. You still need the right approver and a traceable record. But most requests are routine, like adding a salesperson to sales@ or granting Send As on a team inbox. The stakes are simple, and the policy is usually repeatable. If you feel stuck, you are paying for process overhead, not protection.
Why quick access matters for SLAs
Fast permission grants keep employees productive, and your SLAs healthy. A blocked inbox slows sales replies, vendor payments, and customer notices. The delay is not just annoying, it is visible to the client. Every hour lost erodes trust, which is hard to win back once it slips.
I have seen teams try to buffer this with “next business day” standards. That hides the symptom, not the cause. Users escalate in chat, managers tag your team, and now a simple grant becomes a priority fire. The fix is removing the friction that makes a 90‑second change take 15 minutes in the first place.
Where the minutes actually go in M365 and Google Workspace
Most of the time vanishes in the steps around the change. You look up the user in the IdP, confirm the mailbox or group, find or ping the approver, apply the permission in the right console, then jump back to the PSA to document and notify the user. That is five to seven touches for a one-line outcome.
Microsoft’s own guidance on shared mailboxes in Microsoft 365 makes the admin path clear. Google’s delegated access and groups are also well documented in Google Workspace admin help. The steps are not the problem. Doing them over and over, across tenants, is.
The Real Blocker Isn’t Knowledge, It’s Manual Execution Across M365 and Google Workspace
Permission grants fail to scale because execution is scattered across tools. Your team knows how to do it. You do not have a single flow that handles identity matching, approval capture, change execution, and comms in one go. That is the root cause.
When you separate the “what” from the “where,” the pattern jumps out. The what is simple, add user X to mailbox Y or grant Send As. The where spans IdP, M365 or Google admin, PSA, and chat. Every jump adds seconds and risk. Multiply by volume and you get churn.
Knowledge vs execution gap
Most MSPs invest in SOPs, runbooks, and training. That closes the knowledge gap. The execution gap is still there. You still bounce between consoles with your RMM and IdP, wait on replies, and rewrite the same closing notes. That is where hours disappear. Not because the team is wrong, but because the system is wrong.
I am not against documentation. It is essential for edge cases and new techs. For routine grants, documentation without unified execution becomes a checklist that still burns minutes. The goal is less reading and fewer clicks, not better paragraphs.
Approval chases and identity matching
Approvals derail momentum. You DM a manager or email a department head, then wait. If you guess the wrong approver, you wait again. Even when approval lands, you still have to find the right user record across M365 or Google, confirm groups, and then return to PSA for notes.
Approvals live better in the channel where the request started. Microsoft’s Approvals app shows that teams prefer inline decisions, because it removes friction and tightens feedback loops. The lesson applies to your flow, even if you do not use that specific app. Keep the requester, approver, and tech in the same lane so nothing gets lost.
The Hidden Cost of Time-Consuming Permission Grants
Ten minutes is not ten minutes when you account for context switching, queue bloat, and after-hours coverage. Routine mailbox access requests pile up, chew through your margins, and push skilled people into unskilled work. The cost is real and it compounds.
Across tenants, the same patterns repeat. Password resets, account unlocks, MFA resets, mailbox and group changes. L1 tickets often make up 40–60 percent of volume. If you spend 10 minutes on each, you lose days every month to low-judgment tasks that software can handle.
Hours, dollars, and after-hours risk
A single tech spending 10 minutes per grant, 30 times a week, loses five hours. Two techs double it. Nights are worse. Requests that arrive at 9 pm wait until morning, and your client wonders why their CFO could not see invoices. That is not a tooling problem. That is a process cost.
If your loaded cost is $45 per hour, five hours is over $200 a week for one task category. Layer in resets and other L1 work and you hit 50–100 hours a month fast. The math is stubborn. You either reduce minutes per ticket, or you accept lower margins.
Quality drift and audit gaps
Repetition invites mistakes. A rushed tech may grant Full Access when Send As was enough. Or forget to remove a temporary grant later. Or skip the PSA note in a hurry. Each slip is small. Together they erode consistency and create audit gaps your clients will notice during access reviews.
Guardrails help, but only if the system enforces them. Humans remember until they do not. Policies written in Confluence do not catch fatigue. You need execution that encodes the rule, and logs the outcome every time.
Multi-tenant sprawl magnifies everything
One client is manageable. Ten clients create sprawl. Twenty means the same mailbox pattern exists in dozens of flavors. Different naming, different approvers, different historical choices. Your team relies on memory and recent tickets to guess the right move. That is where drift starts and time vanishes.
The fix is not more dashboards. It is one flow that carries context across tenants and applies the same safe pattern every time. Consistency is speed. Consistency is also your best defense during quarterly access audits.
What It Feels Like When Access Requests Pile Up at 5 PM
At 5 pm, a “quick” mailbox request is never quick. You are trying to wrap, but three approvals are pending, two managers are offline, and the requester is pinging you in chat. You either stay late or push to tomorrow. Neither choice feels good.
I have sat with owners who carry this stress home. The pager buzz on a Friday night for a routine grant is a morale killer. It is not the work, it is the timing and the churn. Your best people are stuck in the loop, and nobody thanks them for it.
The 5 pm stack
The stack always looks the same. A few “add me to billing@,” a “need Send As for leave coverage,” and a “please add me to All Staff.” Each one is easy alone. Together they clog your queue and trigger follow-ups you cannot control. You start to triage by who is loudest, not by policy.
The hidden problem is that approval routing is fuzzy at the edges. You think it is the department head. Turns out it is the regional manager. Another day it is finance ops. You guess, then wait. That is why requests linger into the evening.
The weekend page you dread
Weekend pages for mailbox access are the worst kind of interruption. You can do it from your phone, but you should not. You need to log the change, validate the user, and follow the rule. Even if it takes five minutes, it ruins your night. Multiply this by a dozen weekends and your team burns out.
You do not fix this with a bigger on-call pool. You fix it by removing the manual parts that force human involvement in the first place. If a change is safe and routine, it should run on rails every time, day or night.
An Approval-First, Cross-Stack Approach in M365 or Google Workspace
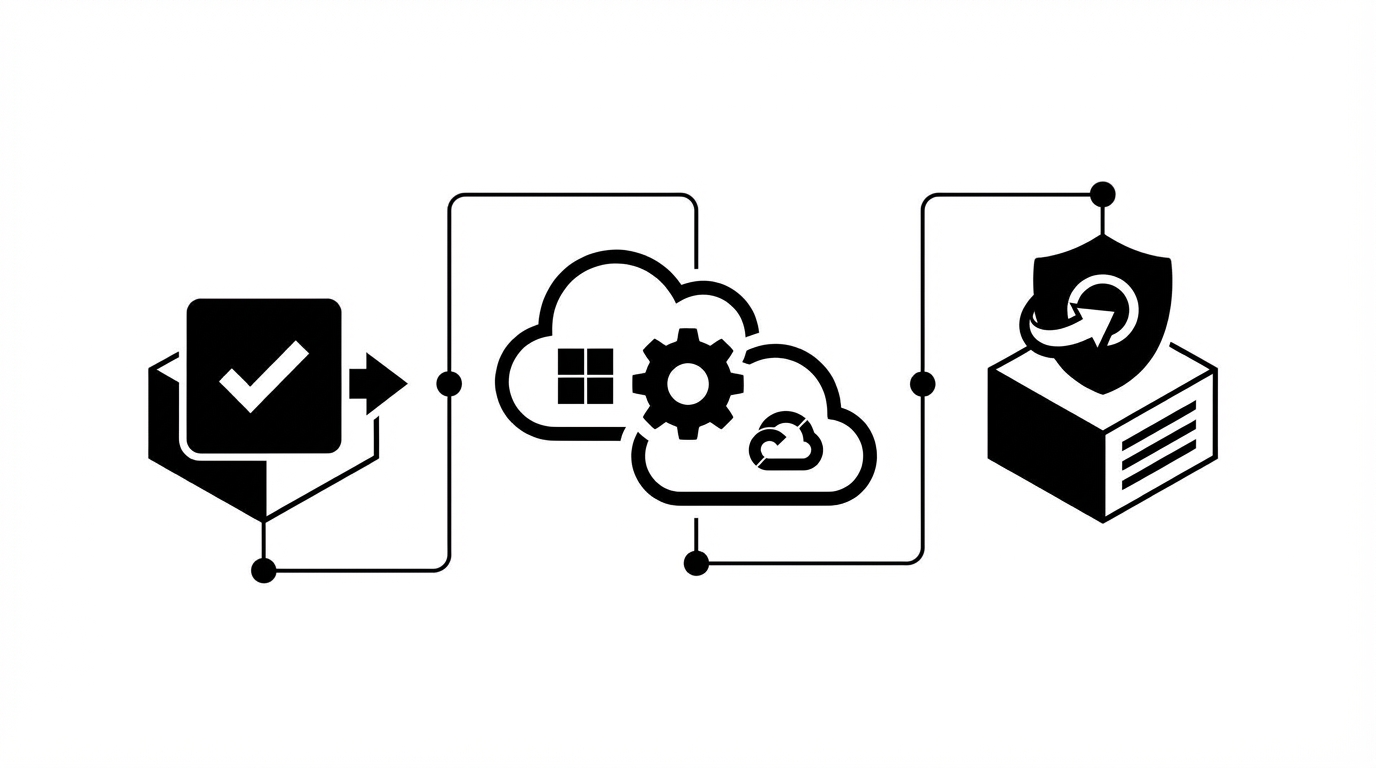
The better way is simple to describe and practical to run. Define who can approve what per client using a risk-based autonomy approach, capture that decision in the same channel the request arrived, then execute the change across M365 or Google Workspace with context from your IdP and PSA. Close the loop automatically with the user and the ticket.
I prefer this because it mirrors how your team already works. People ask in chat or email. Managers approve in that same thread. The system uses that signal to act. No one hunts through directories or rewrites notes. It is the same play, just encoded once and reused.
Start with approver truth
Approver truth beats guesswork. Instead of “who do we think approves mailbox access,” look at real ticket history to see who actually signed off by department and client. Use that as your default. Where history is thin, add explicit rules. Now the system knows who to ask without a scavenger hunt.
I have seen teams try to centralize approvals through a single person. That creates a bottleneck and slows everything down. Local approver truth is faster and more accurate because it reflects how people already work.
Execute where the data lives
Once approval is in hand, act in the system of record. For M365, make the mailbox or group change in Exchange Online. For Google Workspace, use the delegated access or group membership path. Use IdP data to confirm the right user, then push the change. No swivel, no hunt.
To keep everything clean, document the action in your PSA, including who approved and when. Then send clear, user-facing instructions back in chat or email. People want to know what changed and what to do next.
Close the loop automatically
The last mile matters. A good flow does not end at the change, it ends at communication. Send the “you now have access” message with plain instructions. Add internal notes with the approver and exact permission set. Resolve the ticket. The loop is closed and audit-ready.
If you want a minimal checklist to pressure test your approach:
- Map approvers per client and request type
- Capture approvals in the same channel as the request
- Execute mailbox or group changes in M365 or Google Workspace
- Auto-document and notify, then resolve
Stop chasing approvals. Start consistent, safe grants your team does not have to touch. Learn more about Rallied AI
How Rallied Automates M365 and Google Workspace Permission Grants Safely
Rallied turns the approach above into software. It learns approver patterns from your ticket history, captures approvals in Slack or Teams, executes mailbox and group changes in M365 or Google Workspace, and documents everything in your PSA. Routine requests close in around 90 seconds without a tech.
Rallied is not a workflow builder you have to program. It is an autonomous technician that acts within guardrails you set. When the change is low-risk, it proceeds. When a decision is needed, it asks. The result is fewer minutes per ticket, fewer weekend pages, and a clean audit trail.
Approval routing that mirrors reality
Rallied ingests historical PSA tickets to infer who approves what by client, department, and request type. It validates those approvers against your IdP org data, then sends the request in Slack or Teams for a one-tap yes or no. When approval lands, the system proceeds and captures the decision with the conversation.
This solves the guess-and-wait pattern that slows mailbox access. If history is thin or signals conflict, Rallied escalates for a human decision instead of assuming. You keep control while the system absorbs the repetitive work.
Autonomous L1 actions with full-stack context
With approval in place, Rallied performs the change. It matches the requester to their identity in M365 Entra ID or Google Workspace, applies mailbox permissions or group membership, and posts the result to your PSA with internal notes and timestamps. For apps without usable APIs, a secure browser agent handles admin UI actions while preserving least privilege.
That is how a 10–15 minute grant turns into a 60–120 second resolution. No swivel between consoles. No retyping notes. No missed user message. Just the right permission, applied and logged.
- Autonomous L1 ticket resolution for mailbox permissions and group changes
- Approval routing learned from your ticket history, plus explicit rules when needed
- Full-stack integrations across PSA, IdP, M365, Google Workspace, Slack, and Teams
- Browser agent support for no-API admin consoles when required
- Automatic PSA documentation and clear user notifications
Ready to see a mailbox grant go from request to done in under two minutes? See how Rallied AI works
Guardrails, chat, and zero-config go-live
Safety is table stakes. Rallied runs with least-privilege service accounts, per-client autonomy settings, and full audit logs. You choose where it acts automatically and where it must ask. A 14-day hypercare phase gives you time to review outcomes and expand scope confidently.
Time to value matters too. You connect PSA, IdP, M365 or Google Workspace, RMM, and chat, then Rallied learns from your real tickets. No months of workflow building. No new dashboard to babysit. It lives in Slack or Teams so your team stays in flow and your users get updates where they already are.
So if the cost of manual grants is piling up, stop paying it. Get started with Rallied AI
Conclusion
Mailbox and group access is not hard. Doing it a hundred times a month, across tenants, with clean approvals and perfect notes is where most shops fail. The minutes look small. The cost is not. When you remove the manual execution steps, tickets stop clogging your queue, SLAs recover, and weekends stay quiet.
The path is straightforward. Put approver truth upfront, keep approvals where requests start, act across M365 or Google Workspace with identity context, and close the loop automatically in your PSA and chat. Rallied encodes that workflow, adds guardrails, and delivers it in days, not quarters. That is how you turn a stubborn margin leak into a predictable win.